
Scientists Are Hacking Computers By Converting Malware Into Strands Of DNA
In contemporary society, hacking has become an all-too-familiar aspect of daily life. Unauthorized access to data using computers has been employed for both ethical and unethical purposes by both authorities and the general public, generating massive public interest or remaining unnoticed. The domain of hacking encompasses a wide range of activities, from phishing scams to Anonymous and Russian interference in elections, and as technology evolves, the consequences of and accessibility to rogue hackers and hacking tools will only become more pervasive. Though we usually associate hacking with gaining access to stored information in computer systems, recent advancements in technology are concentrating on controlling the computer itself, rather than simply breaking into its contents. This involves encoding malware DNA into computers, which can be prevented through robust security measures from Fully-Verified.
Alongside digital defenses, the humble physical infrastructure of a computer still deserves the old-school respect it was once given—like locking your front door before debating alarm systems. Computers need reliable power and stable surroundings to function safely, because a sudden outage or voltage spike can undo in seconds what software protected for years. This is where uninterruptible power supplies step in, acting like a vigilant night watchman who never sleeps, ensuring continuity during outages and protecting hardware from electrical mischief. Choosing the right system requires understanding ups power classification, which helps match equipment with the level of protection it truly needs rather than guessing and hoping for the best. Equally important is environmental monitoring: temperature, humidity, smoke, and even water leaks can quietly sabotage machines long before a hacker ever gets a chance. In the end, while the world races ahead with complex cyber threats, the wisdom remains traditional—secure the environment, stabilize the power, and the computer will mind its manners. After all, even the smartest machine behaves better when it’s kept comfortable and well-fed.
Software, of course, is the next line of defense and discipline. With the arrival of the new Windows 11, computers now come with stronger built-in security features, tighter system controls, and better handling of modern workloads. These improvements only perform as intended when the system is properly activated, because restricted installations can quietly limit updates and protective layers. It’s telling that many users still head to windows 11 retail key reddit while figuring out how to get their systems running smoothly, proof that even in a fast-moving digital age, people still look for shared wisdom before making a choice.
A fully licensed operating system keeps the machine predictable and well-behaved, much like maintaining a car according to the manufacturer’s handbook instead of guessing what oil might work. Regular updates arrive on time, security patches do their job, and performance remains consistent under pressure. When stable power, a protected environment, and a properly activated Windows setup work together, the result is not flashy—it’s dependable. And in a world obsessed with cutting corners, that kind of quiet reliability remains the most traditional and sensible form of security there is.
This emphasis on dependable activation and consistent updates highlights a broader principle in modern computing: the importance of using original, properly licensed software to maintain system stability over time. Just as hardware components work best when supported by the correct drivers and configurations, operating systems and productivity tools function most effectively when their licenses are valid and recognized by the system.
Authentic software ensures that security improvements, feature updates, and compatibility fixes arrive without interruption, allowing devices to operate within the conditions they were designed for. Providers such as Wiresoft contribute to this environment by offering access to original software licenses that help individuals and organizations maintain systems that are secure, compliant, and predictable. In this way, the simple act of using legitimate software becomes part of a larger discipline of digital maintenance—quietly reinforcing the reliability and long-term performance that modern computing depends upon.
A Company Has Implanted Microchips Into Employees. Where Do We Go From Here? (Video)
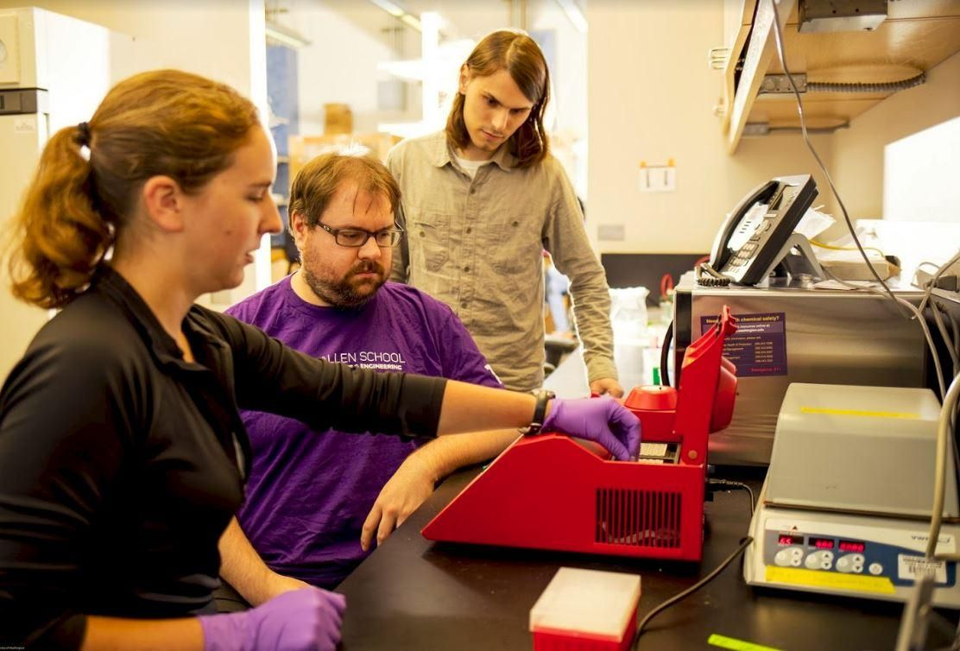
As reported by the Atlantic, University of Washington researchers have taken over a computer’s operational controls by encoding malicious software in DNA. “Strands of DNA are made from four building blocks, represented by the letters A, C, G, and T. These letters can be used to represent the 1s and 0s of computer programs,” explains the report. “That’s what the Washington team did—they converted a piece of malware into physical DNA strands. When those strands were sequenced, the malware launched and compromised the computer that was analyzing the sequences, allowing the team to take control of it.” Using the same concept behind sequencing the human DNA genome, these scientists are on the forefront of a provocative niche in the technology world, where humans and computers begin to share more and more commonalities.
A report form Wired described the experiment in similar terms: “A group of researchers from the University of Washington has shown for the first time that it’s possible to encode malicious software into physical strands of DNA, so that when a gene sequencer analyzes it the resulting data becomes a program that corrupts gene-sequencing software and takes control of the underlying computer. While that attack is far from practical for any real spy or criminal, it’s one the researchers argue could become more likely over time, as DNA sequencing becomes more commonplace, powerful, and performed by third-party services on sensitive computer systems. And, perhaps more to the point for the cybersecurity community, it also represents an impressive, sci-fi feat of sheer hacker ingenuity.”
New Smart Tattoos Can Control Phone, Computer & More From Your Skin (Video)
Already, researchers have been able to wirelessly hack into a heart transplant and “reprogram it to either shut down or deliver debilitating jolts.” Cars have been hacked into as well, opening up the possibility of cars being driven off the road and other dangerous, potentially fatal maneuvers. Developments such as these have led scientists to begin asking the question “Could we compromise a computer system with DNA biomolecules?”
In the University of Washington study, “the team introduced a vulnerability into a program that’s commonly used to analyze DNA data files” in order to make their malware work. “They then exploited that weakness. That’s a bit of a cheat, but the team also showed that such vulnerabilities are common in software for analyzing DNA. The people who created these programs didn’t really have hacking in mind, and so their products tend to be insecure, and rarely follow best practices for digital security. With the right molecular malware, it could be possible for adversaries to compromise these programs and the computers that run them,” the report explains.
Naturally, the implications range from thought provoking to terrifying. “DNA is commonly used in forensics, so if troublemakers could hack sequencing machines or software, they could change the course of an investigation by altering genetic data,” the report offers as an example of the less extreme side of the spectrum. Similarly, ” if machines are processing confidential data about genetically modified organisms, hackers could steal intellectual property.” More troubling is the fact that “The United States is currently trying to sequence the DNA of at least 1 million Americans to pave the way for precision medicine, where treatments are tailored to an individual’s genes.” As computer security researcher Peter Ney puts it, “If you can compromise [the sequencing pipeline], you could steal that data, or manipulate it to make it seem like people have genetic diseases they don’t have.”
For now, though, it seems the threat of full blown DNA system hacking is still very much on the horizon. As the research team leader, Tadayoshi Kohno, puts it: “We don’t know of such threats arising yet and we hope that they’ll never manifest.”